-
Ask Vishy, the personal AI-assistant of Naavi for all your information on Naavi.org
Naavi

IICA Qualified Independent Director

-

-
DGPIN: 4PJ-7T8-FK8P: 12.94018310,77.55421020
-
Plus Code : WHR3+3P
Bing_site_search
Google_site_search
-
Recent Posts
Archives
Archives by Date
-
-
The Collateral Damage..not permitted in the Post Puttawamy scenario
Posted in Privacy
Leave a comment
The Old RTI Provision exposed Data Principals to an Unfair Risk
When an RTI activist picks up information about a Government Scheme for Journalistic Research or Social Audit, it ay acquire sensitive personal information of a large number of public who have given permission to the Government to use the personal information for a specific purpose.
Releasing the information to the journalist my therefore require an assessment
a) Does the release harm the individuals.
b) If so, is the harm outweighs the probable public good.
c) At the time of release, Probable public good is speculative but the harm is definitive and the PIO will take a decision , that can hurt the data principals, for which he is not equipped with.
After the Puttaswamy judgement this is not permitted under law. Hence the need to modify Section 8(1)(j) was mandatory.
Naavi
Posted in Privacy
Leave a comment
Privacy vs. Transparency: Realities of India’s New Data Law
FDPPI has raised some issues against the Challenge filed in Supreme Court on the constitutional validity of DPDPA which is coming up for hearing on 13th May 2026.
Introduction: The Post-Puttaswamy Era
For decades, India’s transparency landscape operated on a relatively simple axis: the citizen’s right to know versus the state’s duty to disclose.
That era ended in 2017.
With the landmark Puttaswamy judgment, the Supreme Court elevated privacy to a fundamental right, sparking a high-stakes tension between the Right to Information (RTI) Act and the new Digital Personal Data Protection (DPDP) Act, 2023.
In the ongoing legal challenge before the Supreme Court, the Foundation of Data Protection Professionals in India (FDPPI) has stepped in as a crucial “middle-ground” expert.
Moving beyond the binary narrative of “Government vs. Petitioners,” this body of scholars and technologists argues that the DPDP Act isn’t an attack on transparency, but a necessary recalibration for a digital-first society.
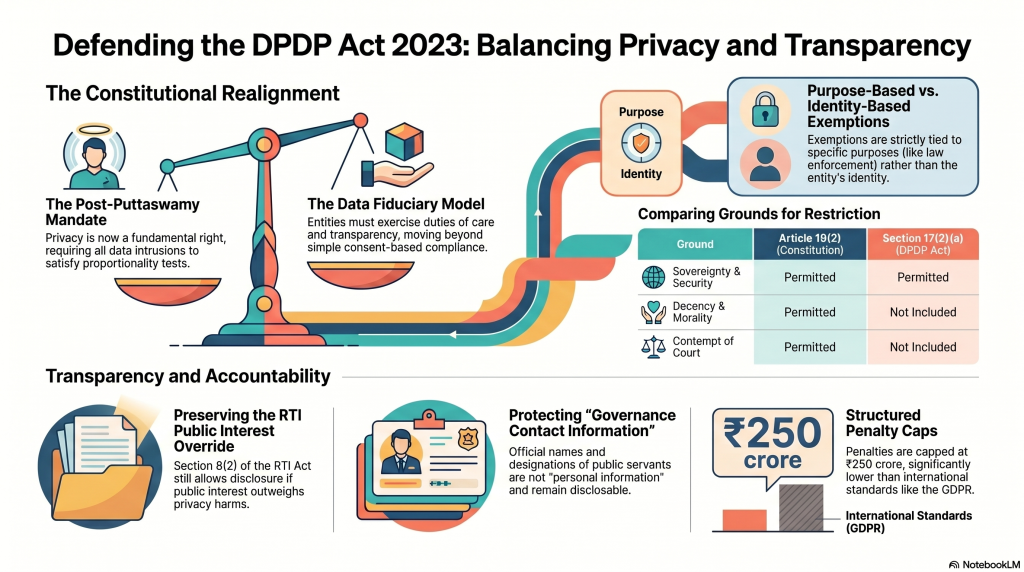
Takeaway 1: Stop Calling it a Blanket Bar—Privacy Decisions Just Got a Promotion
Critics have been quick to label the amendment to Section 8(1)(j) of the RTI Act as a “blanket bar” on the disclosure of personal info.
But a closer look at the FDPPI’s argument suggests a “relocation of decisional responsibility” rather than a shutdown.
The core of the issue is “institutional suitability.
” After Puttaswamy , weighing privacy against transparency requires a complex “proportionality test”—a task for which a mid-level bureaucrat was never equipped.
By moving this decision to higher public authorities under Section 8(2), the law recognizes that balancing two fundamental rights is no longer a routine administrative checkbox .”The unamended Section 8(1)(j) required a Public Information Officer—typically a mid-level administrative functionary… to determine, at first instance, whether disclosure of personal information would cause ‘unwarranted invasion’ of privacy…
After Puttaswamy Juggement, this is constitutional adjudication of the highest order.”
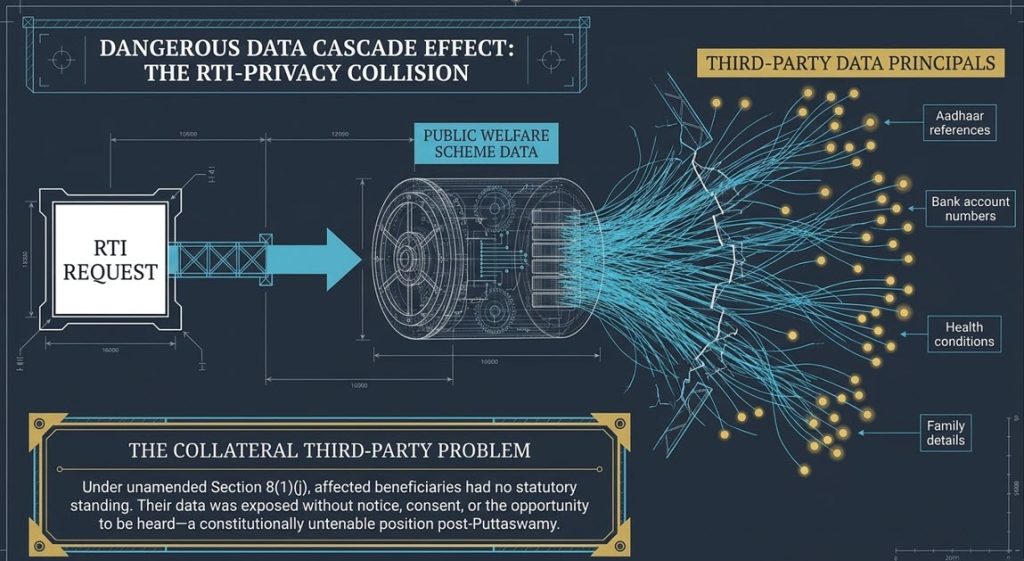
Takeaway 2: Protecting the “Collateral” Citizen
The debate often focuses on the “right to know” about public officials, but it overlooks the “Collateral Third-Party Data Problem.”
When an RTI request targets welfare scheme records, it often inadvertently exposes the sensitive data of thousands of innocent citizens who never consented to being in the spotlight.
FDPPI argues that exposing this data is “constitutionally untenable” under the principle of informational self-determination. These citizens aren’t wrongdoers; they are simply beneficiaries whose data is caught in the crossfire.
The data at risk includes:
-
- Full names and home addresses
- Aadhaar references
- Bank account numbers
- Specific health conditions used for eligibility
- Detailed family records
Takeaway 3: Public Officials Aren’t “Private” (The Governance Distinction)
One of the most persistent fears is that the DPDP Act will serve as a shield for corrupt officials.
However, the FDPPI’s “interpretive suggestion” draws a sharp line between “personal info” and “functional info.
“The law is designed to protect the private lives of individuals, not the “Governance Contact Information” of public functionaries.
Official identities—names, designations, and work emails—are functional, not personal.
Under Section 3(c)(ii), the DPDP Act does not apply to personal data that is made or required to be made publicly available by the individual themselves or under any other law. Since official identities of public servants are already public via gazettes and appointment orders, they remain disclosable.
Takeaway 4: The Journalist’s Purpose-Based Protection
Is the DPDP Act a muzzle for the press?
Not necessarily.
While the Act lacks a categorical “journalist” identity exemption, the FDPPI points out that Section 17(2)(b) creates a “purpose-based” framework.
Processing data for “research, archival, and statistical purposes” is permitted, provided it doesn’t lead to a specific decision about the individual. This covers the “research loop” of investigative and data-driven journalism.
Furthermore, the FDPPI notes that journalists remain accountable through existing safeguards: the law of defamation and professional standards of accuracy and fair comment.
“The Intervener respectfully suggests… the development… of a framework for the registration of accredited journalists—including digital journalists, bloggers and online publishers—with conditional permissions for purpose-specific processing.”
Takeaway 5: “Significant” is a Guardrail, Not a Weapon
The threat of a ₹250 crore penalty has sent shivers through many organizations, but the phrasing of Section 33(1) contains a built-in constraint.
The Data Protection Board can only impose penalties if a breach is “significant.” This term acts as a legal shield, preventing the Board from weaponizing the Act over trivial or technical errors.
Interestingly, despite the headlines, India’s penalty cap is actually more conservative than global benchmarks. For instance, the GDPR allows for fines up to 4% of a company’s global turnover, which can dwarf a fixed ₹250 crore limit.
To ensure fairness, the Board must legally consider these four factors before setting a price tag:
-
- The nature, gravity, and duration of the breach.
-
- The type of personal data affected.
-
- Whether the breach is repetitive.
-
- Mitigation measures taken by the organization.
Conclusion: The Five-Year Evolution
As we look toward full operationalization by May 2027, the DPDP Act provides a “safety valve” in Section 17(5).
This five-year transitional flexibility allows the government to course-correct based on real-world friction.
However, one nuance remains: the controversial deletion of the “proviso” to Section 8(1)(j)—the rule that information shouldn’t be denied to a citizen if it can’t be denied to Parliament.
While the FDPPI defends the privacy recalibration, they notably do not defend the loss of this “informational symmetry” between the electorate and their representatives, suggesting it could be restored without compromising the core privacy framework.
Final Thought: As we move into a future where our digital identities are our primary identities, we cannot afford a transparency regime that doesn’t respect the right to be left alone?
Naavi
Posted in Privacy
Leave a comment
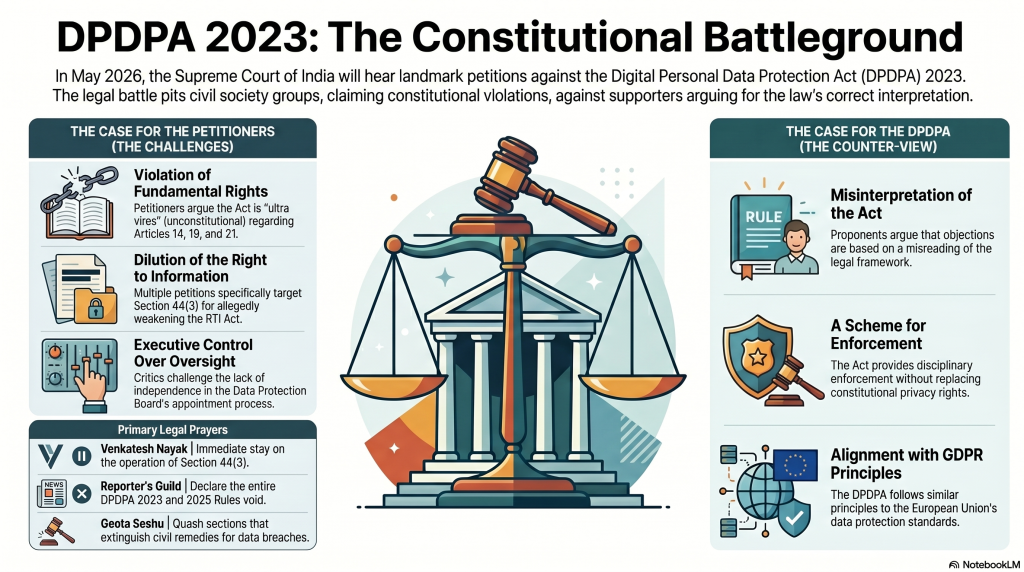
Hearing in Supreme Court on “Scrap DPDPA” demand to resume on 13th May 2026
The petition of Mr Venkatesh Nayak Vs Union of India (WP-C-177/2026) along with the following writ petitions will come up for hearing on 13th May 2026 at the Honourable Supreme Court.
- W.P.(C) No. 212/2026 (PIL-W) (IA No. 51893/2026 – STAY APPLICATION)-National Campaign for Peoples Right to Information
- W.P.(C) No. 211/2026 (X) (IA No. 51414/2026 – GRANT OF INTERIM RELIEF and IA No. 51415/2026 – PERMISSION TO FILE SYNOPSIS AND LIST OF DATES)-Reporter’s Collective-
- W.P.(C) No. 286/2026 (PIL-W) (IA No. 68833/2026 – STAY APPLICATION)-
- W.P.(C) No. 275/2026 (PIL-W) (IA No. 66957/2026 – EX-PARTE AD-INTERIM RELIEF)
Additionally IA No.85635/2026 filed on behalf of FDPPI will also be considered. In the last hearing on 23rd March 2026, the Government was asked to file it’s reply to the petitions so that counters could be filed by other parties.
The four petitions together have serious prayers including scrapping of DPDPA and DPDPA Rule and are argued by a battery of well known advocates including the following:
-
- Ms. Indira Jaising, Sr. Adv. Ms. Mishi Chaudhary, Adv. Mr. Paras Nath Singh, AOR Mr. Prasanth Sugathan, Adv. Mr. Jayant Malik, Adv. Mr. Kabir Darshan Singh, Adv. Mr. Syed Mohammad Haroon, Adv. Mr. Sadeeq Ur Rahman, Adv. Mr. Abhishek Manu Singhvi, Sr. Adv. Muhammad Ali Khan, Adv.
- Mr. Omar Gupta, Adv. Ms. Eesha Bakshi, Adv. Mr. Uday Bhatia, Adv. Mr. Naman Basoya, Adv. Mr. Abishek Jebaraj, AOR A. Reyna Shruti, Adv. Mr. D.P. Singh, Adv. Mr. Prashant Bhushan, AOR Ms. Cheryl D’Souza, Adv. Ms. Anushka Singh,
- Adv. Ms. Vrinda Grover, Adv. Mr. Soutik Banerjee, Adv. Ms. Devika Tulsiani, Adv. Mr. Aakarsh Kamra, AOR Mr. Pritam Singh, Adv. Mr. Umesh Kumar Shukla, Adv. Mr. Shishupal Singh, Adv. Mr. Vedprakash, Adv. Mr. Ankit Bhatnagar, Adv. Mr. Praharsh Chaudhary,
- Adv. Mr. Pawan Kumar Saxena, Adv. Mr. Balajee D. K., Adv. Dr. Mahendra Limaye, Adv. Dr. Tushar Mandlekar, Adv. Mr. Alok Sharma, Adv. Mr. Anand Dubey, Adv. Mr. Raghvendra Kumar, AOR Ms. Harsha Sharma, Adv.
- For Respondent(s) the case will be argued by:
- Mr. Tushar Mehta, Solicitor General Mr. Gurmeet Singh Makker, AOR Mr. Madhav Sinhal, Adv. Mr. Rajat Nair, Adv. Mrs. Shilpa Ohri, Adv. Mr. Mayank Pandey, Adv. Mr. Chander Uday Singh, Sr. Adv. Ms. Cheryl D’souza, Adv. Ms. Bidya Mohanty, Adv. Katyayani Suhrud, Adv. Mr. Abhishek K., Adv. Ms. Anushka Singh, Adv.
For the Intervention petition of FDPPI, (IA No.85635/2026), following advocates will appear.
-
- Dr. Mahendra L.,
- Adv. Dr. Tushar Mandlekar, Adv.
- Mr. Alok Sharma,
- Adv. Mr. Raghvendra Kumar,
- AOR Mr. Devvrat Singh, Adv.
The Bench headed by the honourable Chief Justice along with JUSTICE JOYMALYA BAGCHI HON’BLE MR. JUSTICE VIPUL M. PANCHOLI will hear the case.
The prayers in the three petitions filed by Mr Venkatesh Nayak, Reporter’s Guild and Geeta Seshu are as follows:
Venkatesh Nayak Prayers
In light of the facts and circumstances stated hereinabove, it is most humbly prayed that this Hon’ble Court may be pleased to:
- Direct that the operation of Section 44(3) of The Digital Personal Data Protection Act, 2023, shall be stayed during the pendency of the captioned proceeding
Reporter’s Guild Prayers
It is respectfully prayed that this Hon’ble Court may kindly be pleased to:
- Issue a writ in the nature of mandamus, or any other appropriate writ, order, or direction declaring the whole of the Digital Personal Data Protection Act, 2023, and specifically Sections 5, 6, 8, 10, 17, 18, 19, 36, and 44(3), of the Digital Personal Data Protection Act, 2023, to be void, inoperative and unconstitutional for being ultra vires Articles 14, 19, and 21 of the Constitution;
- Issue a writ in the nature of mandamus, or any other appropriate writ, order, or direction declaring the whole of the Digital Personal Data Protection Rules, 2025, specifically Rules 3, 6, 7, 8, 9, 13, 16, 17, and 23 of the Digital Personal Data Protection Rules, 2025, to be void, inoperative and unconstitutional for being ultra vires Articles 14, 19, and 21 of the Constitution;
- Issue any other writ, order or direction as this Hon’ble Court may deem fit and proper to do complete justice in the circumstances of the case.
Prayers of Geeta Seshu
It is prayed that this Hon’ble Court may be pleased:
- Issue an appropriate writ, order or direction or declaration quashing and setting aside Sections 7, 17(2)(a), 19(3) 24, 36, 44(2)(a), and 44(3) of the Digital Personal Data Protection Act, 2023, to the extent challenged herein, as being unconstitutional, void and inoperative, and violative of Articles 14, 19(1)(a), 19(1)(g), 21 and 21A of the Constitution of India.
- Issue an appropriate writ, order or direction, or declaration quashing and setting aside Rules 5, 6, 17, 18, 21 and 23, and the Second Schedule, Fifth Schedule, Sixth Schedule and Seventh Schedule of the Digital Personal Data Protection Rules, 2025, to the extent challenged herein, as being unconstitutional, void and inoperative, and violative of Articles 14, 19(1)(a), 19(1)(g), 21 and 21A of the Constitution of India.
- Issue an appropriate writ, order or direction, or declaration quashing and setting aside Section 17(2) of the Digital Personal Data Protection Act, 2023, insofar as it empowers the Central Government to exempt any of its instrumentalities from the application of the provisions of the Digital Personal Data Protection Act, 2023 and the Digital Personal Data Protection Rules, 2025. d) Issue an appropriate writ, order or direction, or declaration quashing and setting aside the Second Schedule of the Digital Personal Data Protection Rules, 2025.
- Issue an appropriate writ, order or direction, or declaration quashing and setting aside the Second Schedule of the Digital Personal Data Protection Rules, 2025.
- Issue an appropriate writ, order or direction, or declaration quashing and setting aside Section 44(2)(a) of the Digital Personal Data Protection Act, 2023, insofar as extinguishes the right of affected persons to seek compensation or civil remedy for unlawful processing of personal data and/or data breach.
- Issue an appropriate writ, order or direction, or declaration quashing and setting aside Section 44(3) of the Digital Personal Data Protection Act, 2023 insofar as it dilutes the right to information of the citizens of India.
- Issue an appropriate writ, order or direction, or declaration quashing and setting aside Section 19(3) and Section 24 of the Digital Personal Data Protection Act, 2023 read with Rules 17, 18 and 21 and the Fifth and Sixth Schedules of the Digital Personal Data Protection Rules, 2025, insofar as they relate to the constitution, appointment, service conditions and functioning of the Data Protection Board of India.
- Issue an appropriate writ, order or direction, or declaration directing the Respondent No. 1 to frame a constitutionally compliant mechanism for appointment, tenure and service conditions of the Data Protection Board of India, ensuring its independence from executive control.
- Issue an appropriate writ, order or direction, or declaration quashing and setting aside Section 36 of the Digital Personal Data Protection Act, 2023 read with Rule 23 and the Serial No. 1 of the Seventh Schedule of the Digital Personal Data Protection Rules, 2025.
- Issue an appropriate writ, order or direction, or declaration directing the Respondent No. 1 to incorporate and notify a specific and proportionate exemption under the Digital Personal Data Protection Act, 2023 and the Digital Personal Data Protection Rules, 2025 for processing personal data for journalistic, editorial, investigative and public interest reporting purposes, including protection of journalistic sources. Alternatively, issue an appropriate writ, order or direction, or declaration quashing and setting aside Section 7 of the Digital Personal Data Protection Act, 2023, insofar as it fails to provide an exemption for processing of personal data for journalistic purposes .
FDPPI has already filed an initial request for intervention
Naavi’s views on this regard which is in public domain is available here.
Naavi has also provided a list of suggestions to make DPDPA acceptable to all including the petitioners.
In a nutshell Naavi has expressed the view
a) That the objections raised are borne out of mis-reading of the Act and the Rules
b) That the objections raised are not tenable and do not indicate any constitutional crisis.
c) That some clarifications can be issued by the Government to ally the disproportionate fears expressed by the petitioners.
Under no circumstances, we feel that the Act and the Rules should be scrapped.
Naavi has also indicated that DPDPA 2023 does not claim to protect the Privacy Right and only provides a scheme for enforcement of protection of Personal Data along with an administrative penalty. It leaves ITA 2000 and other laws to work along with DPDPA 2023 to provide relief to the data principals. It also leaves the right to enforce the constitutional right to Privacy outside the reliefs granted by DPDPA 2023 (Which is only related to disciplinary action against Data Fiduciaries in tact. Naavi has also indicated that this is the same principle adopted by GDPR also for the EU region.
We await the further developments.
Naavi
Posted in Privacy
Leave a comment
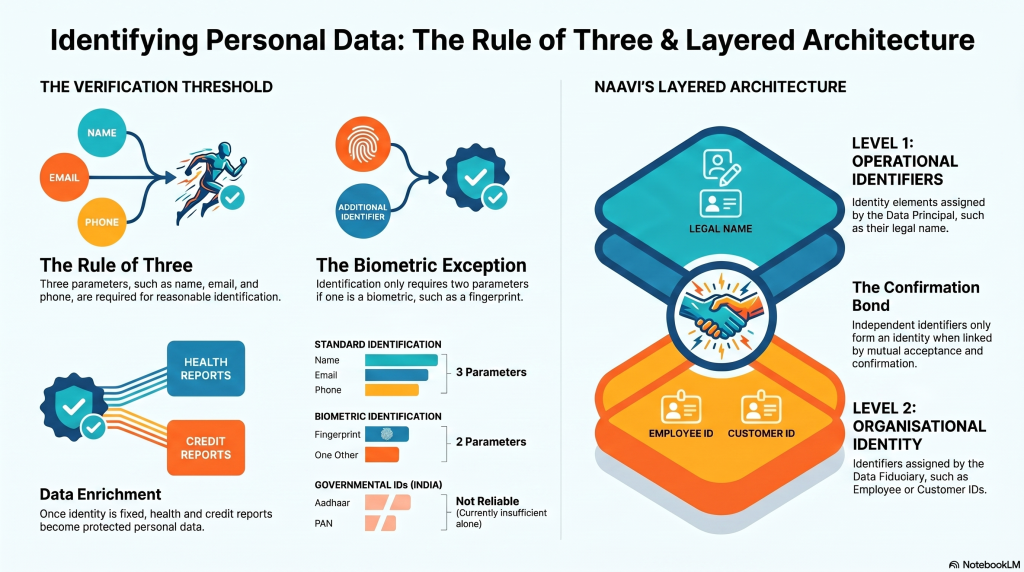
Anatomy of Personal Data
Personal Data is a key corporate asset in this time of Data Driven Business. Organizations collect specific identifiable personal data some times in a structured manner through a form associated with a service request. This is an ideal situation when the entire set of data elements are collected in one shot along with a proper notice, purpose linkage, data minimisation etc.
But in actual practice an organization accumulates individual data elements often not specifically identifiable with a data principal. The “Personal Data identifiers” therefore become available but cannot be associated with any identifiable individual. Even when a “Name is available”, if it is concluded as belonging to a specific person which the Data Fiduciary knows, there could be a risk of mismatch. Hence an organization has to wait for accumulation of at least 2 parameters which together create an identity.
To be on the safer side it is better to have 3 parameters to identify a person unless one of the two parameters happens to be a “Biometric” information.
Under “Biometric” one can take the finger print, the facial photograph, the voice sample, DNA etc.
A Unique Government ID such as an aadhaar number or PAN number could perhaps have been considered equivalent to the biometric for identification but for the current state in India where these are not reliable.
In the absence of such “biometric ” data, there should be atleast 3 parameters such as the name, email and the phone to reasonably identify an individual.
Once the identity of an individual can be fixed with a reasonable certainty, information such as a “Behaviour Profile” or a “Health report”, “Credit Report” can be added to the personal information and will also form the data that needs to be protected under the Data Protection Law.
To capture this nature of Personal Data as a “Set of Data Parameters”, Naavi adopts the following layered approach to recognition of Personal data.
Level 1: Operational Identifier: Name (Assigned by the Data Principal)
Level 2: Organizational Identity: Employee ID, Customer ID (Assigned by the Data Fiduciary).
Level 1+Level 2 will have confirmation from the data principal and the data fiduciary provided the two are linked with acceptance from both. If the two identifiers are present independently they donot form an identity till they are associated with a bond of conformation. This could be through a request for confirmation sent from one of the two to the other and its acceptance by the other.
Level 3: Contact Layer: E Mail address, Mobile number
Level 4: Biometric layer: Finger Print, Facial Photograph, Voice Sample, Dental X ray, DNA etc.
Level 5: KYC layer: A KYC report generated by a trusted third party “Joint Data Fiduciary”
Level 6: Report level: Behaviour Profile, Health Report, Credit Report etc
We can organize these levels into a hierarchical system to move raw data as it flows into an organization into a “Provisional Personal Data Store”, process it periodically and move it to the next level
Naavi
Posted in Privacy
Leave a comment